Block direct access to cloudfront.net URLs when using an alternate domain
If you use AWS’s CloudFront as a straight forward CDN for a static website or simple app, and have an alternate domain set up for that site such as:-
www.yourwebsite.com
instead of
yourwebsite.cloudfront.net
You have likely had issues where some how the cloudfront.net URL for your site has escaped into the wild. This could cause negative SEO issues, due to duplicate content.
After a bit of searching I found that you can use AWS’s WAF service to add an ACL to your CloudFront distribution which will block requests that don’t come from the alternate domain. That’s a lot of acronyms, as we know AWS love them.
WTF are WAF and ACL
Short for Web Application Firewall, WAF can protect various resources on AWS from scenarios like bot attacks more info can be found here.
You can use WAF to create ACLs, or Access Control Lists, which other resources can use to control access, they can even be used to restrict access across many resources.
For our purposes we are going to create a simple custom rule, link it to our cloudfront distribution, so it can allow only requests that come from our alternate domain. Kind of the tip of the iceberg of what you can do with WAF and ACLs.
Setup
Search for “WAF and Shield” on the AWS console.

Then “Create web ACL”

Give your ACL a name and select “CloudFront distributions” as the resource type.

Then we can associate the ACL with a resource, by clicking the “Add AWS resources” searching for your CloudFront distribution and selecting it. This can be done at a later date, or you could use an alternative resource to test before deploying to a live site.

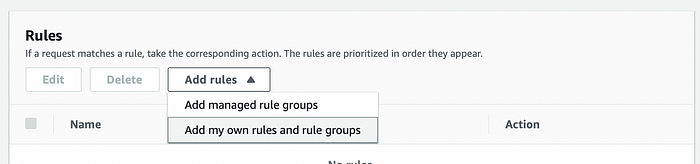
After clicking Next, you’ll be taken to the rules stage, click the “Add rules” button and choose “Add my own rules and rule groups”
We’ll use the “Rule Builder” to create our rule, start by giving it a name and leaving type as “Regular rule”. Then we will build the “if a request…” section as below, with the domain that matches yours, in the “String to match” field.
This is going to check the “Host” HTTP header of an incoming request and make sure it starts with your alternate domain. You could use a regular expression to cover subdomains too.

Then we want to set the “Action” when a request matches this statement, which is simply “Allow” in this instance. Then click add rule.

Now we want to set the default behaviour when the rule isn’t matched, for example when a request came from our something.cloudfront.net domain instead. In this case “Block” requests, which will return a 403 error to requests that don’t match our rule.

After clicking Next, you can leave the “Rule priorities” as default if you only have one rule and click Next. The CloudWatch sampling settings allow you to log info about when your rule have been matched.
After the CloudWatch settings, you can review the ACL and create it, if you associated the CloudFront resource, it will appear on the general settings for the distribution, under the “AWS WAF” section.

If you didn’t associate the ACL to the Distribution, you can edit these settings and select the ACL here too.
Once created and associated a request to your something.cloudfront.net URLs should return a 403 error whilst ones coming from the alternate domain, will be passed through as normal.
